Email is the most common form of web communication in today’s world and over 2 billion active email users are there as it’s convenient and user-friendly. Email provides unique identity to every single user that’s why it is highly targeted by cyber criminals. The most common method used by hackers to access the company important files is by sending them fake emails with malicious links or attachments. And in today’s world, one security breach can put your organization important details and all finances at stake. Let’s understand how to make your email to avoid hacking:
Suspicious Links in Emails or attachments:
Phishers send email with a link or attachments which contains malicious links. The best way to avoid this by not clicking on those links. Instead, hover the cursor over the link and the actual link will be shown and you can check whether it matches the given link. Or go to the official website of the company in the link to verify whether information matches with official site. Generally, it’s not good to open the links or attachments which contains only links without any context.
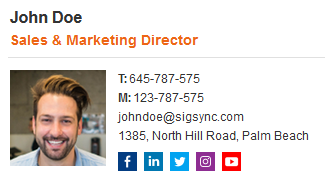
Free Email Signature generator
Free online HTML Email Signature Generator that helps to create professional and visually compelling email signatures by adding your logo, brand colors, contact details and etc.,Secure password and two-factor authentication:
You can avoid the risk by having unique passwords for all of your online services. After setting up the passwords for your accounts, you can also set up two-factor authentication for added security and this important for preventing unauthorized password resets.
Archive Emails:
Archiving your emails over a period of time you can either use dedicated software or any other email system to set up archiving which moves all those emails from your server. you can access the archived through your workstation but limits access for outsiders or it can’t be accessible outside office.
Use different emails for work and personal use:
Never use same email address for work and personal use which in turn helps the hackers to extract all your personal and professional information in one attack. For an instance, if a hacker learns about your online search habits and may send the suspicious email which looks legitimate, if you in case click the link it may help the hacker to get the access over your corporate system.